When OPSEC Meets the Treadmill: The Enduring Threat of 'StravaLeaks': A Comprehensive Guide

Introduction
In January 2018, the cybersecurity and defense communities were confronted with an unprecedented and entirely modern operational security (OPSEC) failure. The fitness tracking application Strava released its Global Heatmap, a beautifully rendered data visualization of billions of user activities worldwide. While it was intended to showcase a global community of runners and cyclists, open-source intelligence (OSINT) analysts quickly noticed a glaring vulnerability: the heatmap brightly illuminated the patrol routes, exercise yards, and treadmill locations of military personnel in highly classified, remote forward operating bases.
This phenomenon, dubbed "StravaLeaks," fundamentally altered our understanding of data exhaust. It proved that the aggregation of seemingly innocuous, anonymized telemetry data could dismantle highly guarded state secrets. Years later, the threat persists. As wearable technology becomes more ubiquitous and fitness applications more deeply integrated into our daily lives, the intersection of physical fitness and operational security remains a highly contested battleground.
This comprehensive guide explores the enduring threat of StravaLeaks. We will delve into the mechanics of geospatial telemetry leaks, analyze why OPSEC doctrines struggle to adapt to the Internet of Things (IoT), and pivot into a practical engineering solution. By the end of this article, you will learn how to build a robust TypeScript-based OPSEC auditing tool designed to sanitize, geofence, and analyze GPX data, ensuring that your organization's digital footprint does not compromise its physical security.
What is When OPSEC Meets the Treadmill?
Operational Security (OPSEC) is a systematic, proven process that identifies, controls, and protects generally unclassified evidence associated with sensitive operations and activities. Historically, OPSEC involved shredding documents, concealing troop movements, and maintaining strict radio silence. However, the digital era has introduced a massive blind spot: consumer-grade wearable devices.
"When OPSEC meets the treadmill" refers to the inherent conflict between human habits (the desire to track fitness goals, share achievements, and measure biometric data) and the strict requirements of operational security. A soldier running laps around an unlisted airfield is generating high-fidelity geospatial intelligence. Even if the individual's profile is anonymized, the "Pattern of Life" (PoL) analysis allows adversaries to deduce the existence, layout, and operational tempo of a secure facility.
The enduring threat of StravaLeaks is not merely about a single app; it represents a systemic vulnerability in how telemetry data is collected, aggregated, and brokered. Modern wearables track coordinates, elevation, heart rate, and timestamps down to the millisecond. When uploaded to cloud ecosystems, this data becomes part of a broader dataset that malicious actors can exploit.
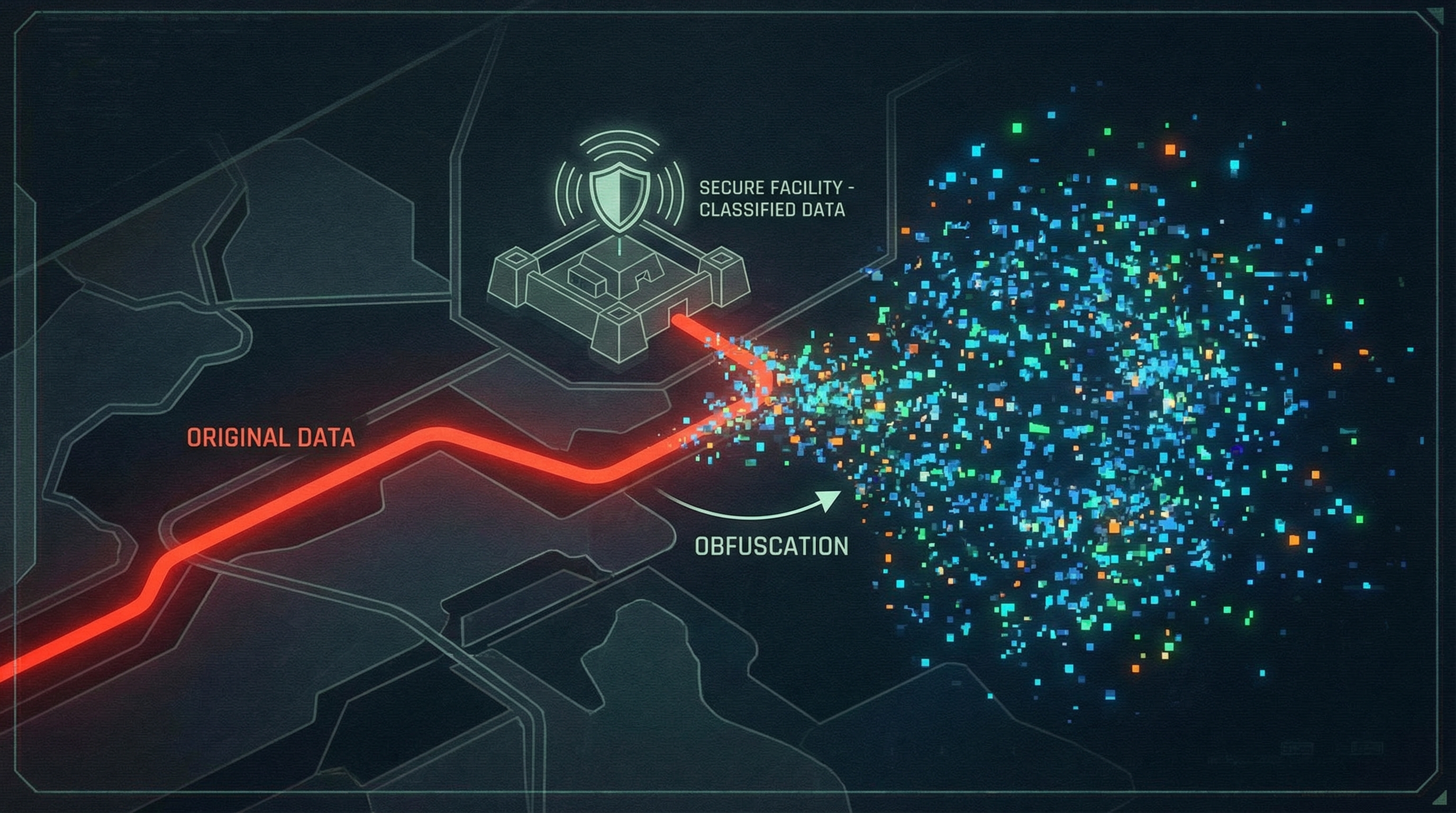
For engineers and security professionals, this presents a unique challenge. We can no longer rely solely on policy ("do not wear smartwatches") because policies are frequently broken. Instead, we must engineer technical solutions that intercept, audit, and sanitize this data before it ever reaches a public server. This requires a deep understanding of geospatial programming, API interception, and data obfuscation techniques.
Key Features and Capabilities
To effectively combat the StravaLeaks phenomenon, organizations must deploy programmatic OPSEC defenses. A robust telemetry OPSEC auditing system must bridge the gap between human behavior and data security. By building a custom TypeScript-based auditing engine, we can intercept and analyze fitness data (typically in GPX or TCX formats) before it poses a threat.
Below are the core capabilities such a system must possess.
Geospatial Geofencing and Intersect Analysis
The cornerstone of any OPSEC fitness auditor is the ability to define sensitive zones (geofences) and determine if an activity intersects with them. By leveraging geospatial libraries, the system can parse a user's route and check it against a secure database of classified or sensitive polygons. If a track falls within a restricted zone—such as a military base, an intelligence facility, or a secure corporate campus—the system flags the file for quarantine or automatic deletion.
Temporal Pattern Recognition
OPSEC is not just about where you are, but when you are there. Adversaries use Pattern of Life (PoL) analysis to determine operational tempos. For example, if guard shift changes occur at 06:00, and a flurry of fitness activity begins exactly at 06:15 every day, the adversary has learned valuable intelligence. An advanced auditing tool can analyze timestamps across multiple files to detect predictable routines and issue warnings about temporal predictability.
Geospatial Fuzzing and Anonymization
Rather than outright banning fitness trackers, a more elegant solution is data fuzzing. This feature involves mathematically altering the starting and ending points of a route, stripping precise timestamp metadata, and rounding coordinate precision. By applying a "fuzzing radius" using the Haversine formula, the system obscures the exact origin of a route (e.g., a specific barracks building or safehouse) while preserving the overall distance and pace metrics the user cares about.
Automated Metadata Stripping
Fitness files contain extensive metadata, including device serial numbers, software versions, heart rate data, and exact timestamps. This metadata can be used to fingerprint specific users across multiple anonymized datasets. A robust OPSEC tool programmatically strips XML or JSON metadata from the telemetry payload, ensuring only the bare minimum required data is exported, if any export is permitted at all.
Installation and Setup
To demonstrate how we can programmatically defend against StravaLeaks, we will build a TypeScript-based OPSEC Auditor. This tool will parse GPX files, apply geofencing rules, and execute data obfuscation.
We will utilize Node.js, TypeScript, and a few powerful geospatial libraries to accomplish this. The primary library we will use is @turf/turf, an advanced geospatial analysis engine for JavaScript, alongside xmldom to parse the GPX XML structure.
First, initialize a new Node.js project and install the required dependencies:
# Initialize a new Node project mkdir opsec-treadmill-auditor cd opsec-treadmill-auditor npm init -y

Install the necessary runtime dependencies
npm install @turf/turf xmldom @xmldom/xmldom
Install TypeScript and type definitions as development dependencies
npm install -D typescript @types/node ts-node @types/xmldom
Next, initialize the TypeScript configuration. This ensures our compiler strictness is set up correctly for enterprise-grade security tools.
```bash
npx tsc --init
Open the generated tsconfig.json and ensure the following core settings are enabled. This configuration provides the strict typing necessary when dealing with sensitive geolocation data structures.
{ "compilerOptions": { "target": "ES2022", "module": "CommonJS", "rootDir": "./src", "outDir": "./dist", "strict": true, "esModuleInterop": true, "skipLibCheck": true, "forceConsistentCasingInFileNames": true }, "include": ["src/**/*"] }
Create your source directory and your main entry file:
mkdir src touch src/index.ts touch src/geofence.ts touch src/obfuscator.ts
Your environment is now ready. In the following sections, we will implement the practical code that brings these OPSEC defenses to life.
Practical Examples
Now that our environment is configured, we will build three distinct modules for our OPSEC auditor. These examples represent real-world use cases for intercepting and securing fitness telemetry.
Example 1: Parsing GPX Data for Analysis
The first step in securing fitness data is parsing the highly nested XML structure of a GPX file. GPX (GPS Exchange Format) is the industry standard for fitness trackers. Our parser will extract the coordinates so they can be fed into our geospatial engine.
import { DOMParser } from '@xmldom/xmldom'; import * as turf from '@turf/turf'; /** * Parses a raw GPX XML string and converts it into a Turf.js LineString Feature. * This allows us to perform advanced mathematical operations on the route. */ export function parseGpxToLineString(gpxString: string): turf.Feature<turf.LineString> | null { try { const parser = new DOMParser(); const doc = parser.parseFromString(gpxString, "text/xml"); const trackPoints = doc.getElementsByTagName('trkpt'); const coordinates: [number, number][] = []; for (let i = 0; i < trackPoints.length; i++) { const point = trackPoints[i]; const lat = parseFloat(point.getAttribute('lat') || '0'); const lon = parseFloat(point.getAttribute('lon') || '0'); // Turf.js expects coordinates in [longitude, latitude] order if (lat !== 0 && lon !== 0) { coordinates.push([lon, lat]); } } if (coordinates.length < 2) { console.warn("Insufficient track points for a valid route."); return null; } return turf.lineString(coordinates); } catch (error) { console.error("Failed to parse GPX data:", error); return null; } }
Example 2: Implementing Restricted Geofences
With our data successfully converted into a Turf.js LineString, we can now perform the most critical OPSEC check: determining if the route intersects with a restricted area. In this example, we define a polygon representing a sensitive military installation and check if the user's run entered that zone.
import * as turf from '@turf/turf'; /** * Checks if a given fitness route intersects with any classified or restricted zones. * Returns true if an OPSEC violation is detected. */ export function detectOpsecViolation(route: turf.Feature<turf.LineString>): boolean { // Define a polygon representing a restricted area (e.g., Forward Operating Base) // Coordinates are [longitude, latitude] const restrictedZone = turf.polygon([[[ [38.8977, 34.8010], // Top Left [38.9050, 34.8010], // Top Right [38.9050, 34.7950], // Bottom Right [38.8977, 34.7950], // Bottom Left [38.8977, 34.8010] // Closing point ]]]); // Check for boolean intersection // If the line string crosses into the polygon, an intersection exists const isViolating = turf.booleanIntersects(route, restrictedZone); if (isViolating) { console.warn("OPSEC ALERT: Telemetry data intersects with a classified geofence!"); } else { console.log("Route cleared: No intersections with restricted zones."); } return isViolating; }
Example 3: Geospatial Fuzzing and Privacy Zones
If the data does not intersect with a highly restricted zone, we still want to apply best OPSEC practices by obfuscating the exact start and end points of the user's route. This prevents adversaries from pinpointing the user's exact residence or specific building within a larger compound. We achieve this by clipping the first and last few hundred meters of the track.
import * as turf from '@turf/turf'; /** * Truncates the start and end of a route to obscure exact locations. * @param route The original LineString route * @param clipDistance The distance to clip from start and end in kilometers */ export function applyPrivacyZones(route: turf.Feature<turf.LineString>, clipDistance: number = 0.5): turf.Feature<turf.LineString> | null { const totalLength = turf.length(route, { units: 'kilometers' }); // If the run is too short to apply privacy zones, reject it entirely for safety if (totalLength <= clipDistance * 2) { console.warn("Route too short to safely obfuscate. Discarding data."); return null; } // Slice the line from the start privacy distance to the end privacy distance const safeRoute = turf.lineSliceAlong(route, clipDistance, totalLength - clipDistance, { units: 'kilometers' }); console.log(`Applied privacy zones. Original length: ${totalLength.toFixed(2)}km, New length: ${turf.length(safeRoute).toFixed(2)}km`); return safeRoute; }
Advanced Use Cases
The fundamental examples provided above form the backbone of a telemetry auditing system. However, in an enterprise or military context, the scale and complexity of the OPSEC threat require much more advanced implementations. Let us explore some power-user features and edge cases that elevate this system from a simple script to a comprehensive security platform.
Fleet-Wide Aggregate Heatmap Analysis
Individual routes are only part of the problem. The true danger of StravaLeaks lies in aggregate data. An advanced OPSEC system must simulate the creation of its own internal heatmap to spot macro-level vulnerabilities. By overlaying thousands of "cleared" routes on top of each other, security teams can detect emergent patterns that are invisible at the individual level.
For example, if multiple soldiers use a supposedly "safe" running path outside a base, the aggregate data will eventually draw a glowing line pointing directly to the base's hidden entrance. TypeScript tools can be written to aggregate these line segments, apply a density clustering algorithm, and alert administrators when a previously safe route becomes too "hot."
CI/CD and Mobile Device Management (MDM) Integration
An OPSEC auditing tool is useless if it is not enforced. Advanced implementations integrate these TypeScript modules directly into an organization's Mobile Device Management (MDM) profiles or a Zero Trust network architecture.
By routing all outbound traffic from fitness applications through an internal proxy or API gateway, the organization can intercept the raw GPX payloads in transit. The API gateway can utilize our TypeScript logic via a serverless function (e.g., AWS Lambda). If an OPSEC violation is detected, the gateway drops the packet and sends a push notification to the user, reminding them of security protocols. This creates an automated, invisible shield against accidental leaks.
Counter-OSINT and Decoy Telemetry Generation
In highly specialized threat environments, defensive OPSEC is not enough; active deception is required. Power users can reverse-engineer the obfuscation logic to generate fake telemetry data. By mathematically synthesizing GPX tracks using randomized pathfinding algorithms constrained to public roads, organizations can upload "chaff" data. This pollutes the public datasets, making it mathematically impossible for adversary OSINT analysts to separate the genuine military personnel signatures from the synthetic noise.
Comparison and Ecosystem Context
When evaluating solutions for the StravaLeaks problem, it is important to understand where custom TypeScript auditing tools fit within the broader ecosystem of operational security and data privacy.
Commercially available fitness applications have attempted to address these concerns since the 2018 incident. Platforms like Strava and Garmin now offer native "Privacy Zones" and the ability to hide the start and end of activities. However, relying on these native tools presents a massive OPSEC risk. Native privacy controls are opt-in, rely entirely on the end-user remembering to configure them properly, and crucially, they still transmit the raw, unredacted data to the company's centralized cloud servers before the privacy filter is applied. If the platform suffers a data breach, the raw telemetry is exposed.
In contrast, adopting a custom interception and auditing approach—like the TypeScript system we built—shifts the security perimeter left. By validating, sanitizing, and blocking telemetry before it leaves the organizational network or device, we remove the reliance on third-party cloud security.
This approach is best utilized in highly regulated environments (defense contractors, military units, intelligence agencies, and elite corporate security teams). While it requires engineering overhead to maintain the geofence databases and manage the proxy infrastructure, it provides absolute, cryptographic certainty that operational locations are not being broadcast to global fitness networks.
Conclusion
The phenomenon of StravaLeaks fundamentally shifted the paradigm of operational security. It demonstrated that in a hyper-connected world, the most dangerous intelligence gathering does not always come from satellites or spies, but from the aggregated data exhaust of our daily routines. When OPSEC meets the treadmill, the stakes are incredibly high, and traditional physical security doctrines are no longer sufficient.
As technical professionals, we have a responsibility to architect systems that protect our users from themselves. By understanding the mechanics of geospatial telemetry and leveraging modern web technologies like TypeScript and Turf.js, we can build robust, automated defenses that intercept and sanitize sensitive data before it becomes open-source intelligence.
The code examples and architectures discussed in this guide provide a foundational blueprint for protecting organizational security in the age of IoT. Your next actionable step is to audit your organization's current telemetry policies. Implement technical guardrails, begin mapping your sensitive geofences, and ensure that the digital footprints of your personnel are not leading adversaries straight to your front door.